Focus on the vulnerabilities that actually matter
Your team focuses on real risk, not scanner noise. bifrost gives you runtime protection and intelligent CVE prioritization — so you know exactly what's exposed, what's protected, and where to act.
Protect
Automatically generates and enforces tailored runtime profiles per container. No code changes. No manual configuration.
Prioritize
Correlates known CVEs against real runtime behavior. Unreachable code paths and blocked vectors are deprioritized automatically.
Prove
Show stakeholders your real attack surface. Measurable security improvement that updates with every deployment.
From Scanner Noise to Actionable Risk
Your scanners report every known CVE across code, dependencies, and images. bifrost uses runtime behavior to show you what actually matters.
Runtime context turns thousands of theoretical vulnerabilities into a focused list of real risks. Your team knows exactly where to start.
By the numbers
Why teams choose bifrost
Less CVE noise
Up to 90% reduction — runtime context separates real risk from theoretical
Code changes needed
Deploy in minutes — drop-in integration with your stack
Continuous protection
Runtime profiles update with every deployment, not quarterly
See it in action
Runtime intelligence at a glance
CVE noise, eliminated
See exactly which CVEs matter based on real runtime behavior. Thousands become dozens.
Learn how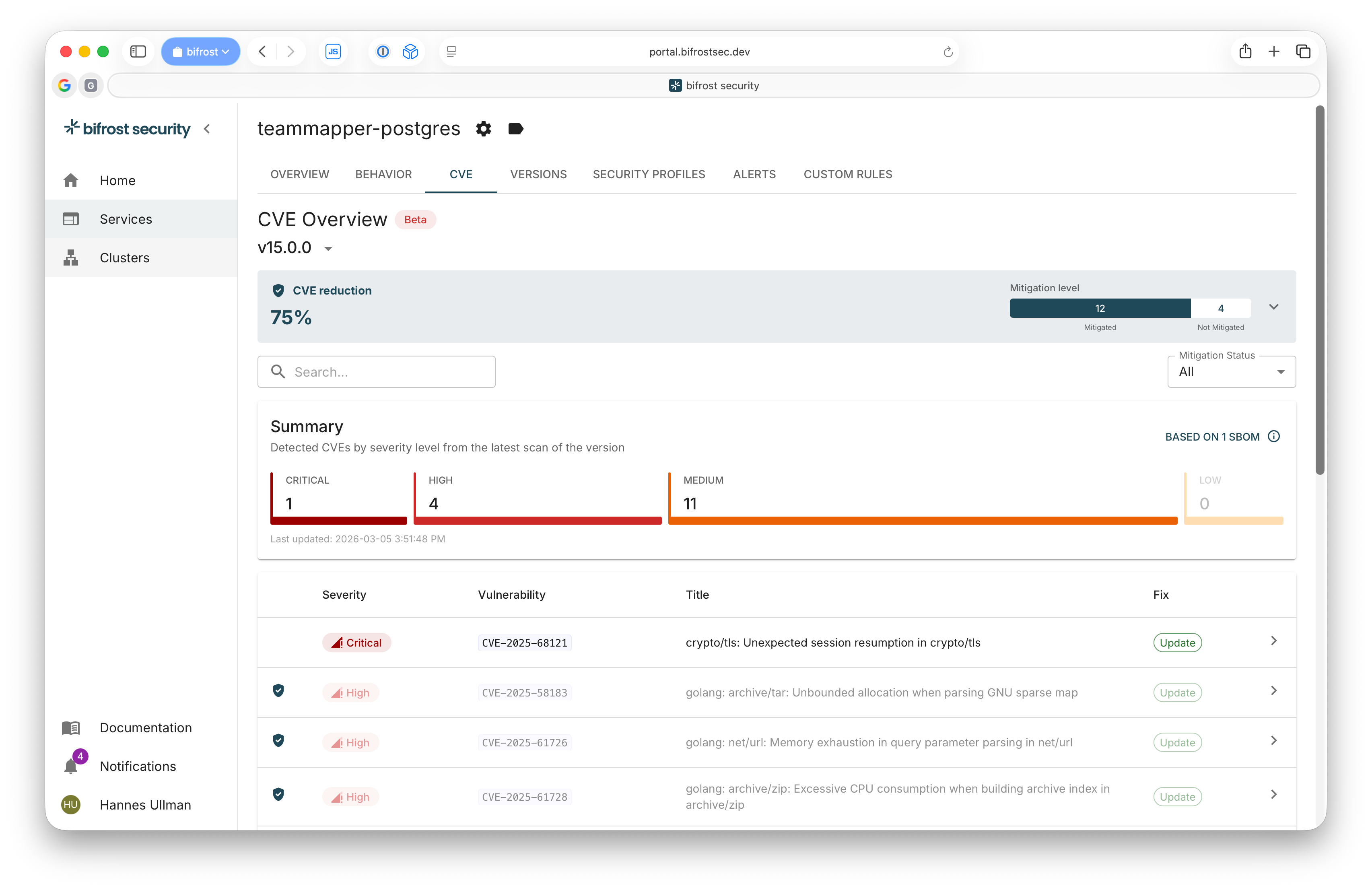
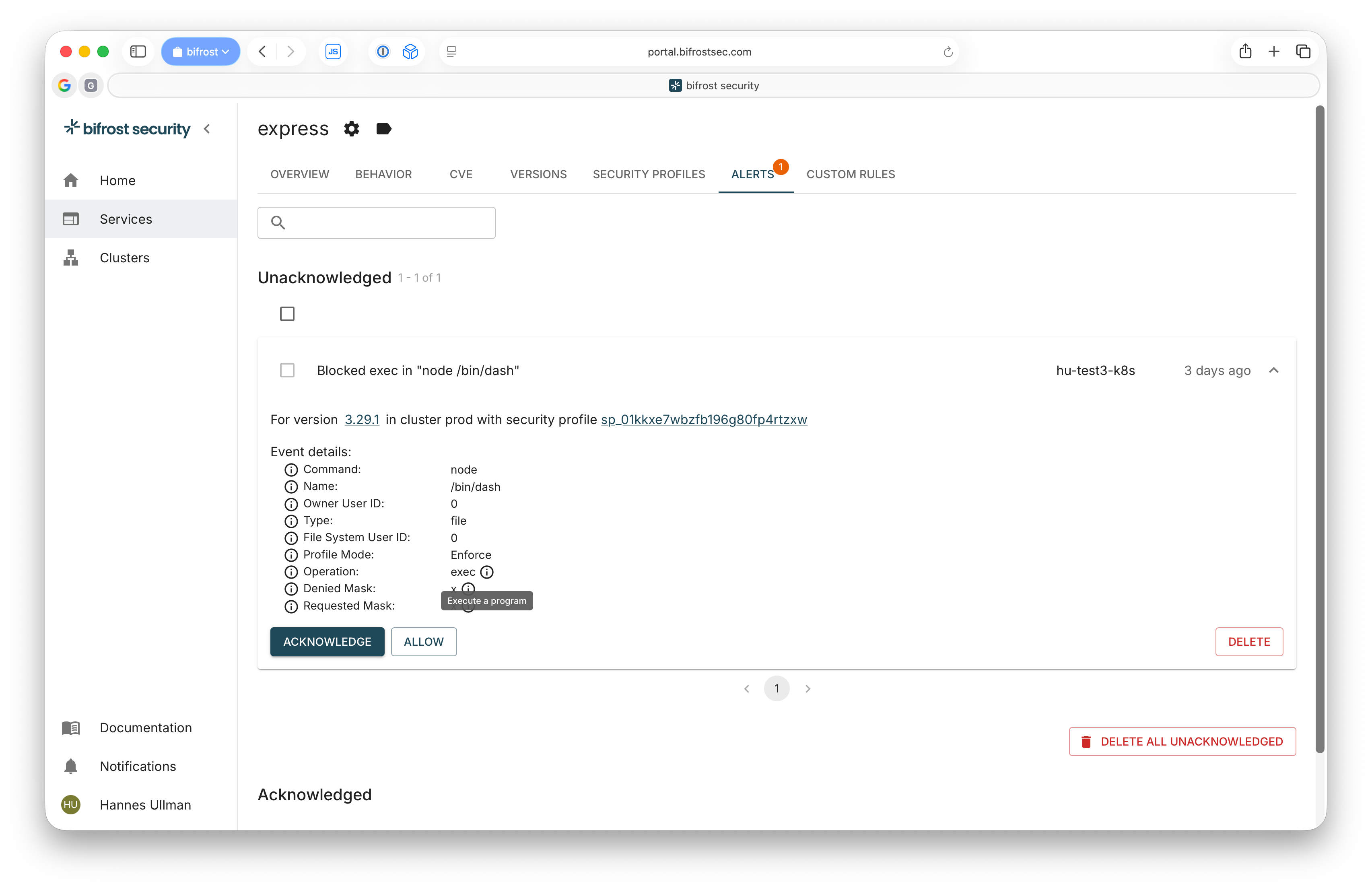
Threats blocked in real time
Runtime profiles catch and block unauthorized behavior before it becomes an incident.
Learn howDeep workload visibility
Understand exactly what each container does — system calls, file access, network connections.
Learn how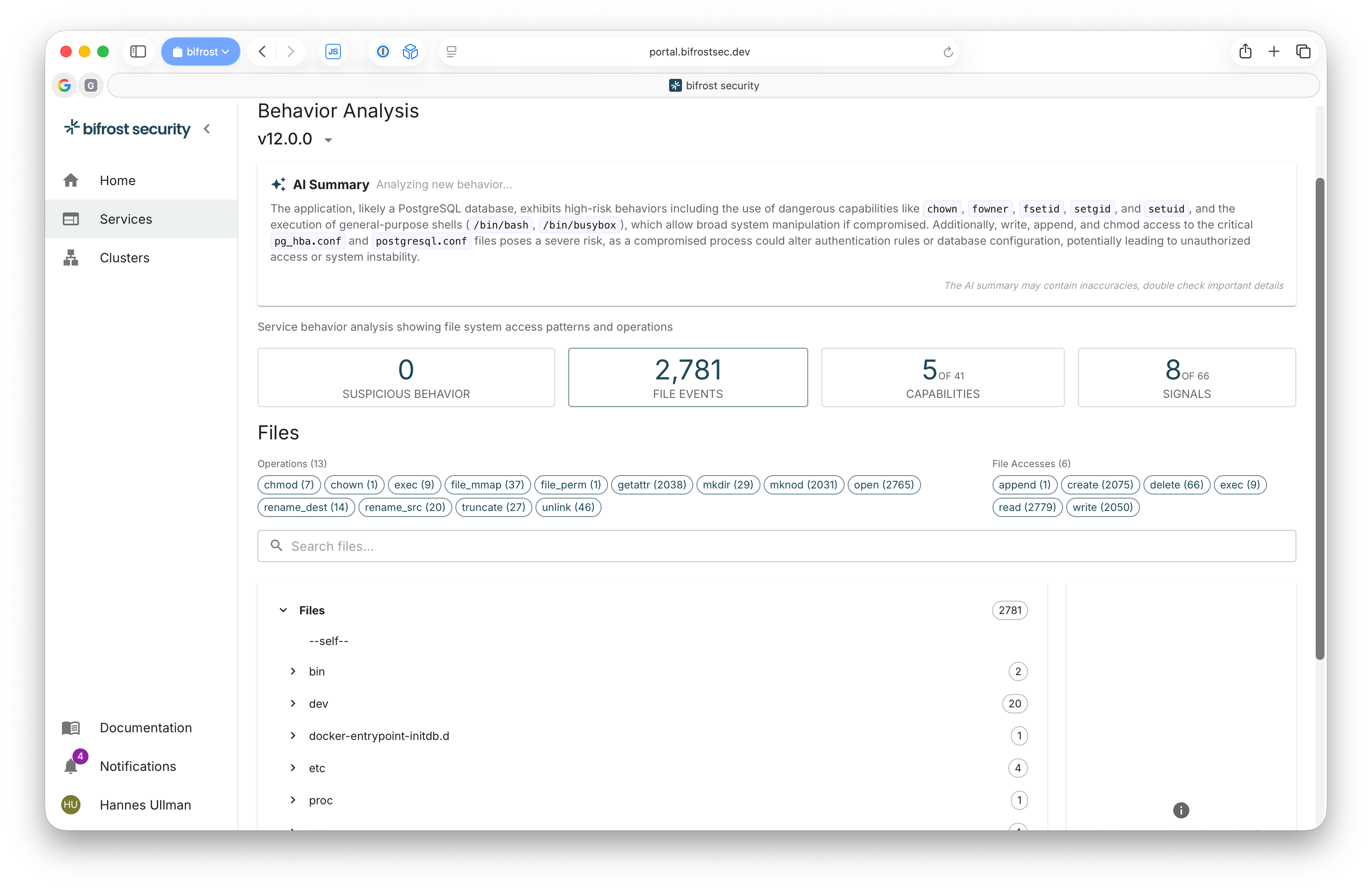
Without runtime context, you're flying blind
Scanners flag thousands of CVEs. CVSS scores tell you everything is critical. Your team spends weeks triaging — but without knowing what actually runs in production, most of that work is wasted.
78%
of CVEs in container images are not exploitable when you check if the code path is actually reachable at runtime
38%
of all CVEs are rated high or critical by CVSS — yet only 2–7% are ever exploited in the wild
600h
per year spent by the average security team just deciding what to fix — not actually fixing anything
Without runtime intelligence, teams fall back on detection and monitoring — tools that alert after something goes wrong. CVSS scores alone can't tell you which vulnerabilities are reachable, which dependencies are loaded, or which containers have more permissions than they need.
bifrost adds the missing layer. Runtime context turns theoretical risk into a focused, actionable list — automatically.
Stay Updated
Subscribe to get the latest on runtime security and exposure intelligence.
Thanks! You're subscribed.
Something went wrong. Please try again.
How bifrost Works
An autonomous loop that observes, protects, and prioritizes — continuously, as your applications evolve.
Observe
bifrost agent learns how each container actually behaves — system calls, file access, network activity — in test and staging environments.
Protect
Automatically generates and enforces tailored runtime profiles per container. Only observed behavior is allowed — everything else is blocked.
Prioritize
Ingests your SBOM data and maps known CVEs to actual runtime behavior. Vulnerabilities in unused code paths or behind blocked syscalls are automatically flagged as low priority.
Works With Your Stack
bifrost integrates seamlessly with the tools and platforms you already use. Deploy on a Kubernetes cluster or use Docker, regardless of where it runs.
Kubernetes
Platform
Docker
Platform
Google GKE
Cloud
Azure AKS
Cloud
OVHcloud
Cloud
AWS EKS
Cloud
DigitalOcean
Cloud
GitHub Actions
CI/CD
ArgoCD
GitOps
Helm
Packaging
Talos Linux
Operating System
Ubuntu
Operating System
Debian
Operating System
appArmor
Security
eBPF
Security
And many more... Don't see your setup here? Let's connect and we'll see how we can support it!
Stop drowning in CVE noise.
Get runtime protection, intelligent CVE prioritization, and measurable security improvement. Free trial, no credit card required.