Autonomous Security. From Runtime Up.
bifrost learns how your applications actually behave, generates protection automatically, and uses runtime intelligence to cut through CVE noise. Security that works without you.
How bifrost Works
An autonomous loop that observes, protects, prioritizes, and evolves — continuously, as your applications change.
Observe
bifrost agent learns how each container actually behaves — system calls, file access, network activity — in test and staging environments.
Protect
Automatically generates and enforces tailored runtime profiles per container. Only observed behavior is allowed — everything else is blocked.
Prioritize
Ingests your SBOM data and maps known CVEs to actual runtime behavior. Vulnerabilities in unused code paths or behind blocked syscalls are automatically flagged as low priority.
Evolve
Profiles and risk assessments update continuously with every deployment. Your security posture adapts as your applications change.
What This Means
Autonomous security that delivers 90% fewer CVEs to triage from day one.
Up to 90%
less CVE noise
Runtime context separates real risk from theoretical. Your team focuses on vulnerabilities that actually matter.
Zero
manual policy management
Profiles generate and evolve automatically. No hand-written rules, no policy drift, no maintenance burden.
Day one
protection
No lengthy configuration or tuning period. Deploy the agent, observe in staging, enforce in production.
Continuous
not periodic
Security updates with every deployment, not quarterly scans. Your posture stays current as your applications change.
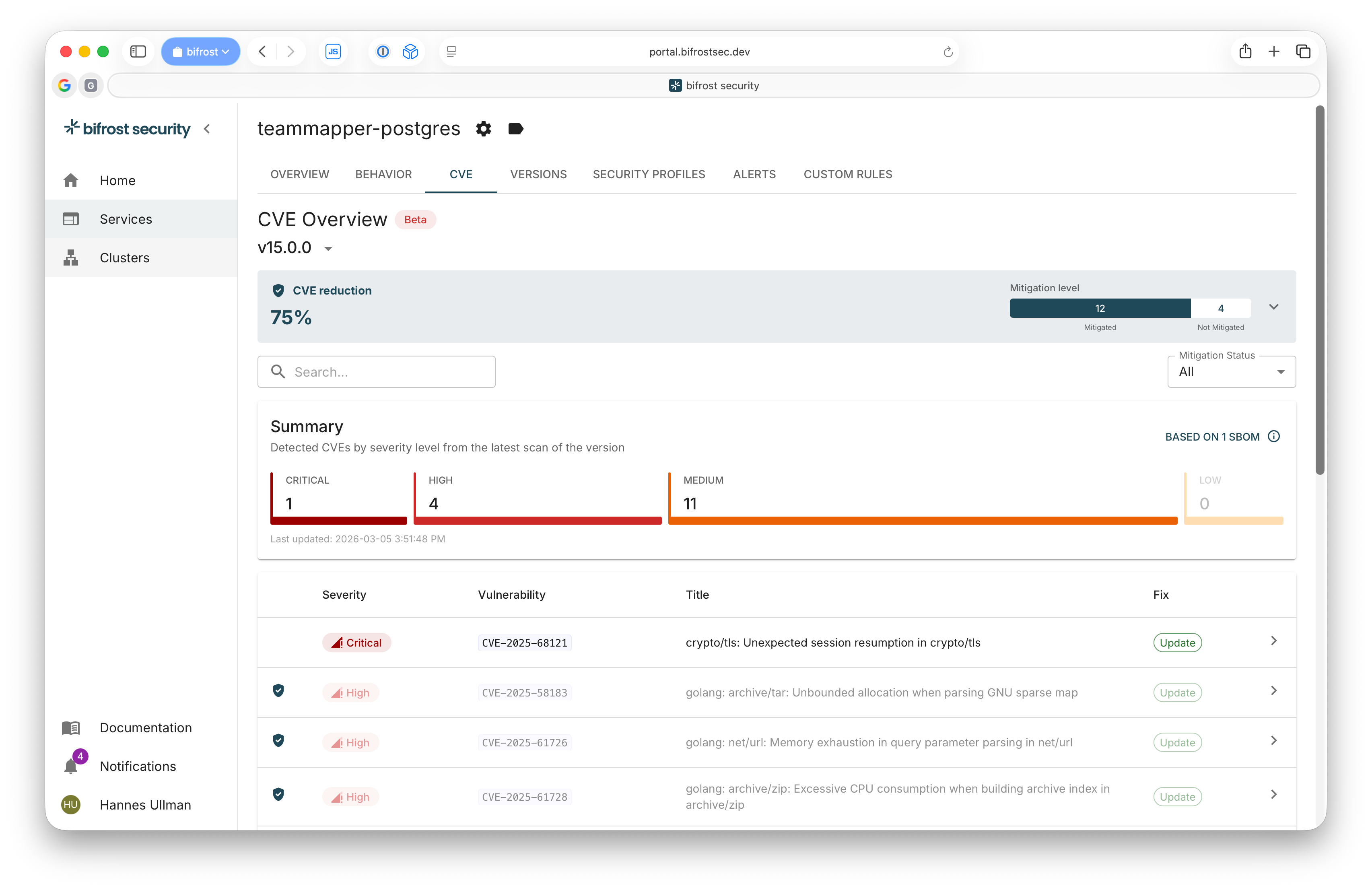
CVE Prioritization
CVE noise, eliminated
bifrost ingests SBOMs at every deployment across your entire lifecycle — from staging to production. We continuously scan them against known vulnerabilities, so you always know exactly what's running and what's exposed. When a new CVE drops, bifrost tells you instantly whether it affects your live workloads — and whether your runtime profiles are already blocking the attack vector.
- SBOMs ingested every deploy — always an up-to-date picture of what's live
- Continuous scanning — new CVEs matched against your production inventory automatically
- Know immediately if a new vulnerability is already mitigated by your runtime profile
- Up to 90% less CVE noise — focus on what's actually reachable and unprotected
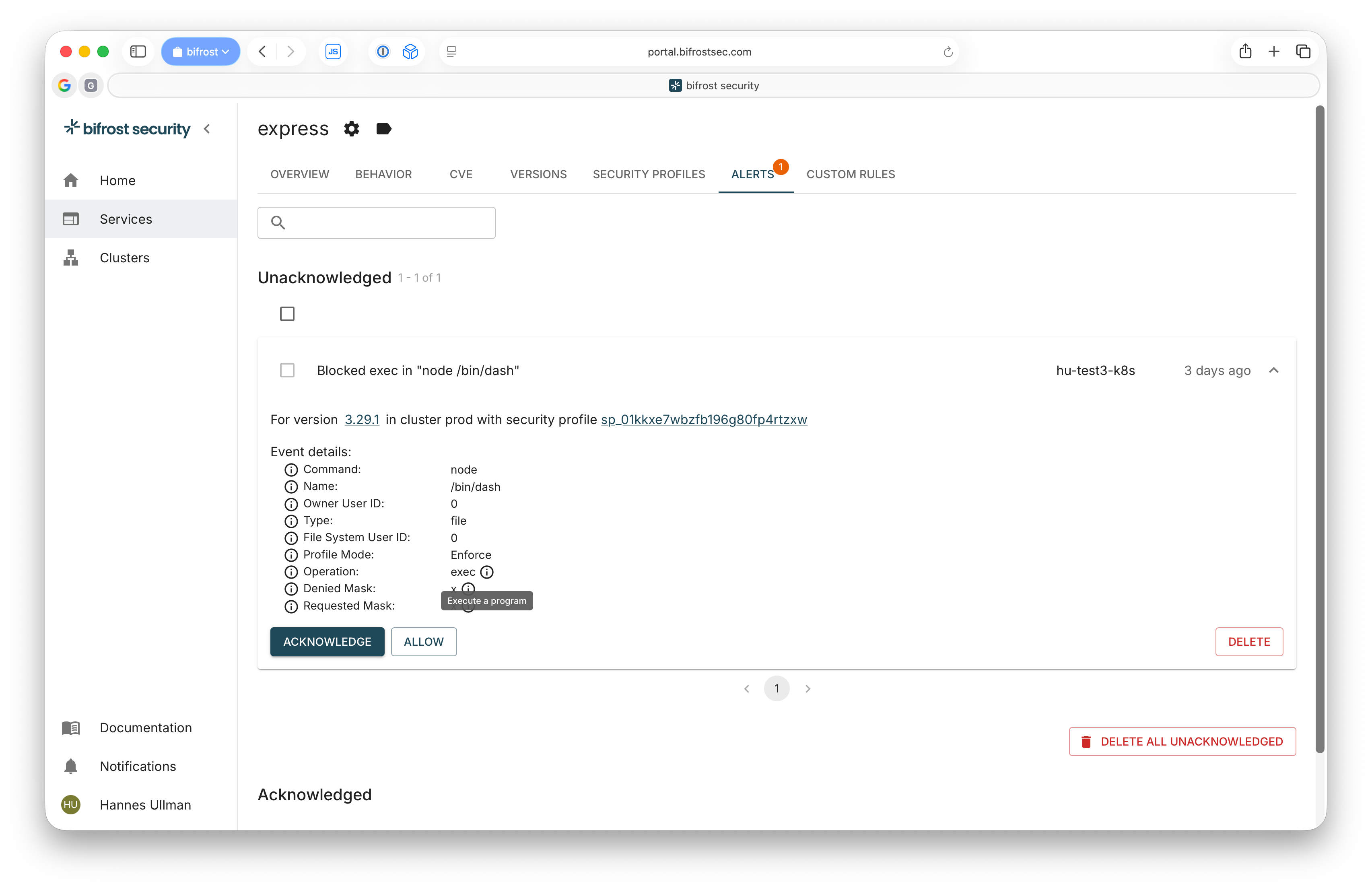
Runtime Protection
Threats blocked in real time
bifrost learns what each container is supposed to do — then enforces it at the kernel level. Unauthorized system calls and file access are blocked before they become incidents. Every blocked event generates a detailed alert, ready to feed directly into your SIEM and central SOC.
- Profiles generated automatically from observed behavior — zero manual policy writing
- Kernel-level enforcement via AppArmor LSM — blocks unauthorized system calls and file access
- Rich, detailed alerts on every blocked event — full context on what happened and why
- SIEM-ready integrations — pipe alerts straight into your SOC workflow
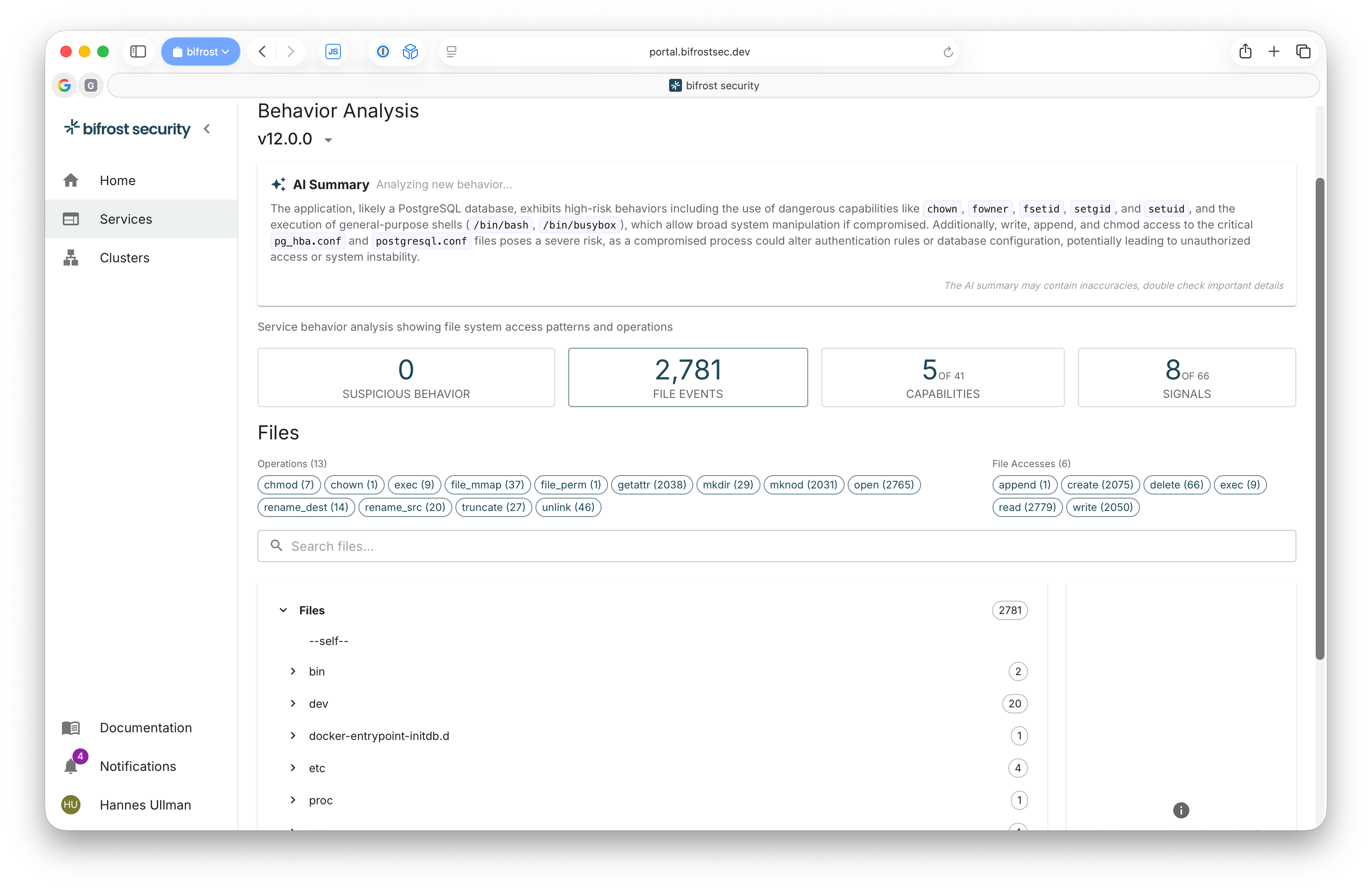
Workload Visibility
Deep workload visibility
bifrost maps the actual behavior of every container — system calls, file access, process activity. Developers spot unwanted behavior early. Security teams see which services carry the largest behavioral footprint — and therefore the biggest attack surface. The result is a real, data-driven foundation for risk assessments and threat modelling across your organization.
- Complete behavioral profile per container — system calls, file access, and process activity
- Spot unwanted or unexpected behavior before it reaches production
- Understand which services have the largest attack surface based on real behavioral footprint
- Data-driven input for risk assessments and threat modelling — not guesswork
bifrost vs Traditional Scanners
Scanners tell you what could happen. bifrost tells you what will actually happen — and blocks unauthorized behavior automatically.
| Capability | Traditional Vulnerability Scanners | bifrost Runtime Security Platform |
|---|---|---|
| CVE Detection | Yes — finds all known CVEs | Yes — finds all known CVEs |
| Reachability Analysis | No — assumes worst case | Yes — uses real runtime behavior |
| Automatic Mitigation | No — manual patching only | Yes — runtime profiles block many vectors |
| Prioritization | By CVSS score only | By exploitability + runtime context |
| Noise Level | High (hundreds/thousands) | Low (focused, actionable list) |
| Continuous Updates | Periodic scans | Every deployment, continuously |
Built for Production
bifrost is designed for enterprise-grade deployments. Minimal resource overhead, maximum protection and intelligence.
Enforcement
AppArmor LSM
Deployment
DaemonSet
Resource Usage
< 200MB RAM per node
Performance Impact
< 1%
SBOM Formats
CycloneDX, SPDX
CVE Correlation
Continuous, real-time
Platform Architecture
Pre-prod Clusters
Production Clusters
bifrost Engine (EU hosted)
Integrations
Trusted by Security-Conscious Teams
Built on research, engineered for production, hosted where your data belongs.
Research-Founded
Born from a joint EU research project at Lund University, then shaped into a product by engineers with real-world production experience. Research depth, practical edge.
EU-Hosted
All data processed and stored in the EU. GDPR-compliant by design. Self-hosted option soon
Swedish-Owned
Researched, developed, and funded by Swedish individuals. A European champion in application security — patented runtime profiling technology, built for the world.
Kernel-Level Enforcement
Built on AppArmor — a battle-proven Linux Security Module trusted in production for 20+ years. Enforcement at the kernel means stronger isolation and inherent protection of sensitive data.
Your security is our security
bifrost is built with data minimization and privacy at its core.
Data minimization
The bifrost agent collects behavioral metadata — system calls, file access patterns, network connections — never application data or personal information.
EU data residency
All data is processed and stored within the EU. GDPR-compliant by design.
Encryption
All data in transit and at rest is encrypted.
Minimal-privilege agent
The bifrost agent runs as a read-only DaemonSet with minimal privileges. No access to your application data.
NIS2-ready
Runtime profiles and continuous CVE prioritization help meet NIS2 requirements for technical security measures and incident prevention.
SOC 2
SOC 2 Type II certification in progress. Contact us for our current security documentation.
Stop drowning in CVE noise.
Get runtime protection, intelligent CVE prioritization, and measurable security improvement. Free trial, no credit card required.